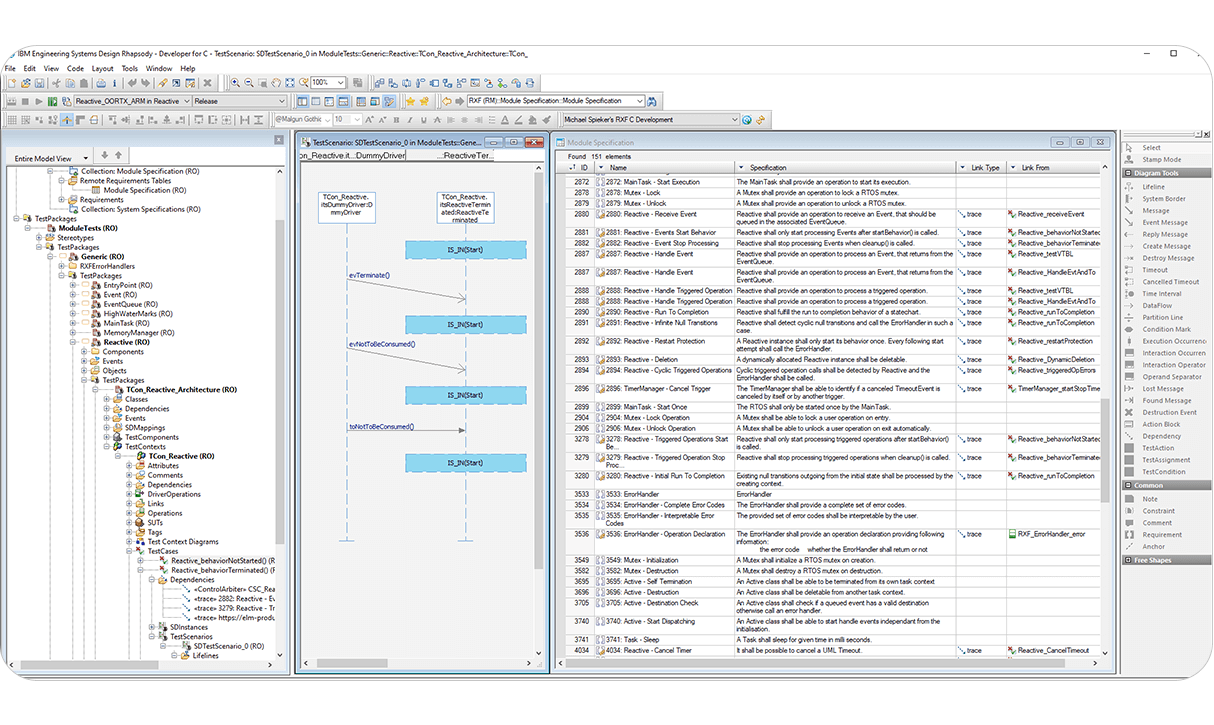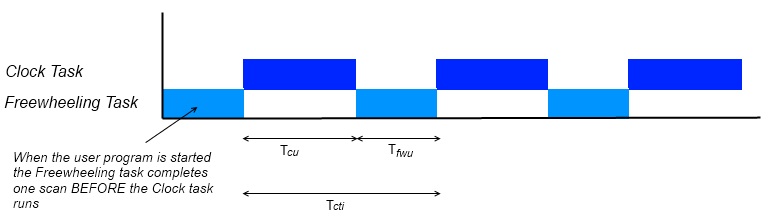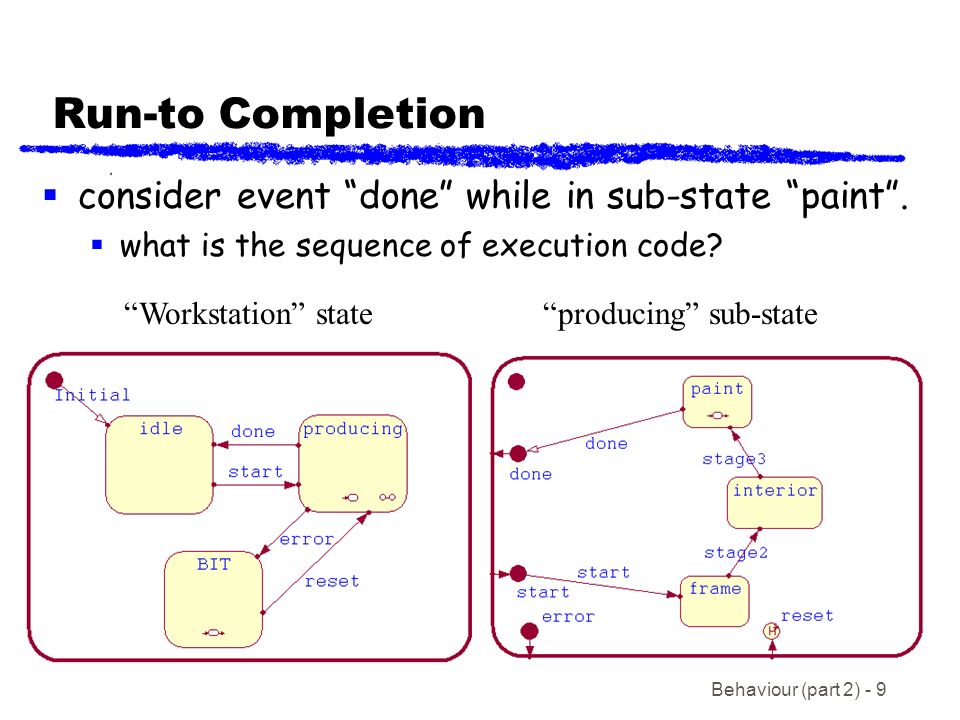
Real Time Systems Advanced State Machines. Behaviour (part 2) - 2 Outline Simple and Composite States Transition Segments and Junction Points Run -to-Completion. - ppt download
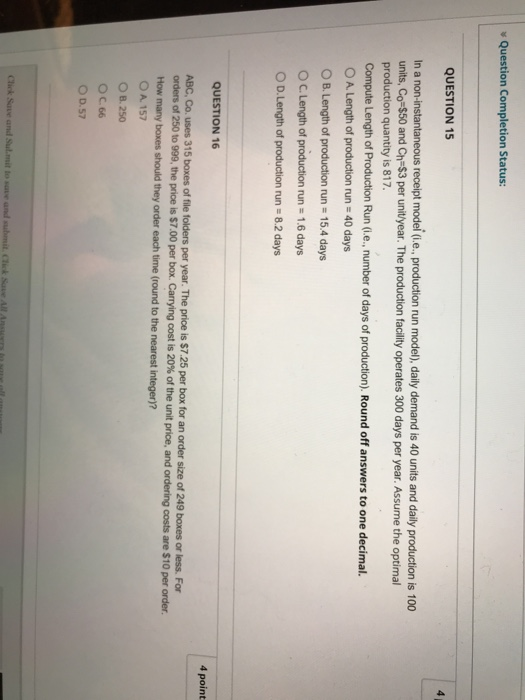
The Short-Run Mirror-Image Teaching Model: Exploring the Relationship between the Phillips Curve and the AD-AS Model - Paul Daniel Poast, 2001

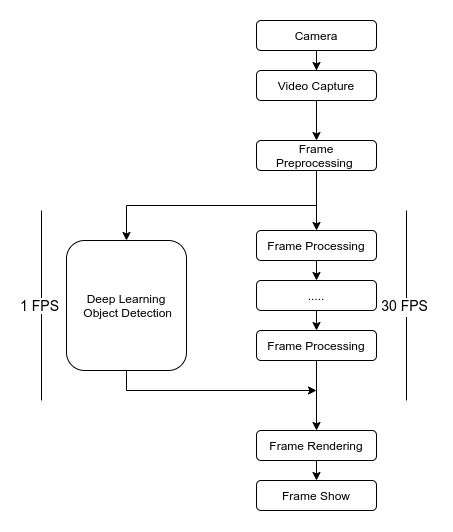
Run-To-Completion Thread Model for Software Bypass Fail Open for an Inline Intrusion Protection System - diagram, schematic, and image 04

Accumulated slip during one model run showing slip status at 25 per... | Download Scientific Diagram
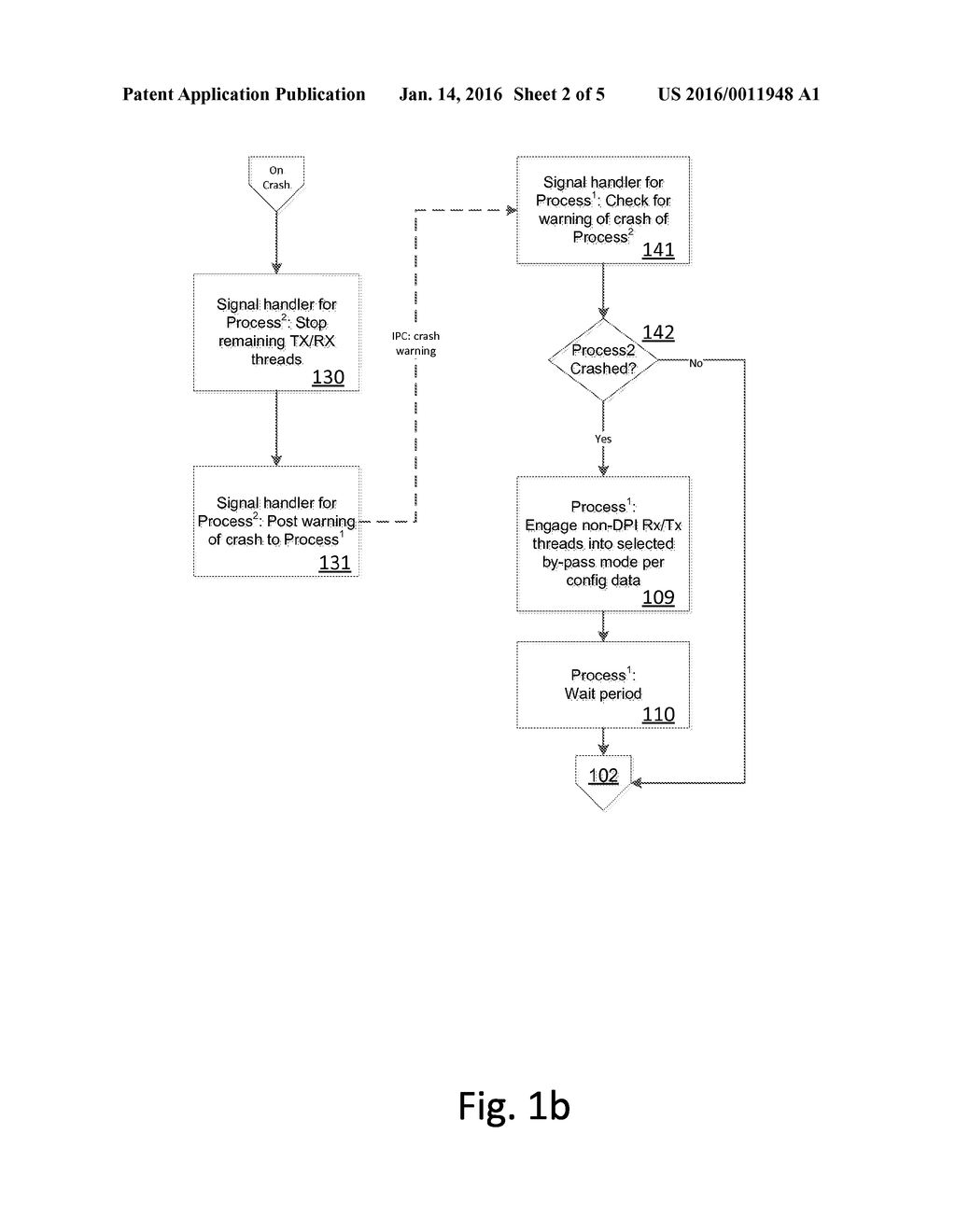
Run-To-Completion Thread Model for Software Bypass Fail Open for an Inline Intrusion Protection System - diagram, schematic, and image 03

Run PyTorch Lightning and native PyTorch DDP on Amazon SageMaker Training, featuring Amazon Search | MKAI

Completion times for one progress cycle requirement in the El Teniente... | Download Scientific Diagram