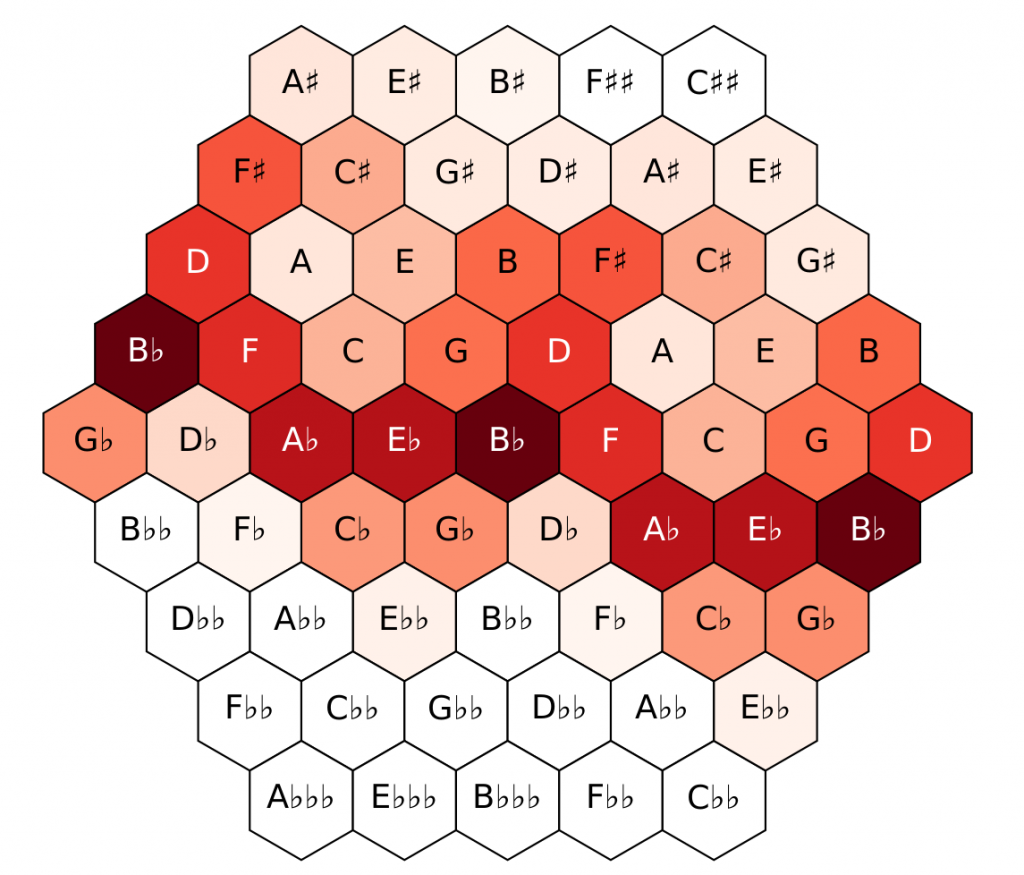
Amazon.com: JIUFOTK Musician Knowledge Metal Sign Vintage Music Studio Decor The Periodic Table Of Music Notation Tin Poster Club Home Office Room Wall Decoration Plaque 12x16 Inches: Posters & Prints
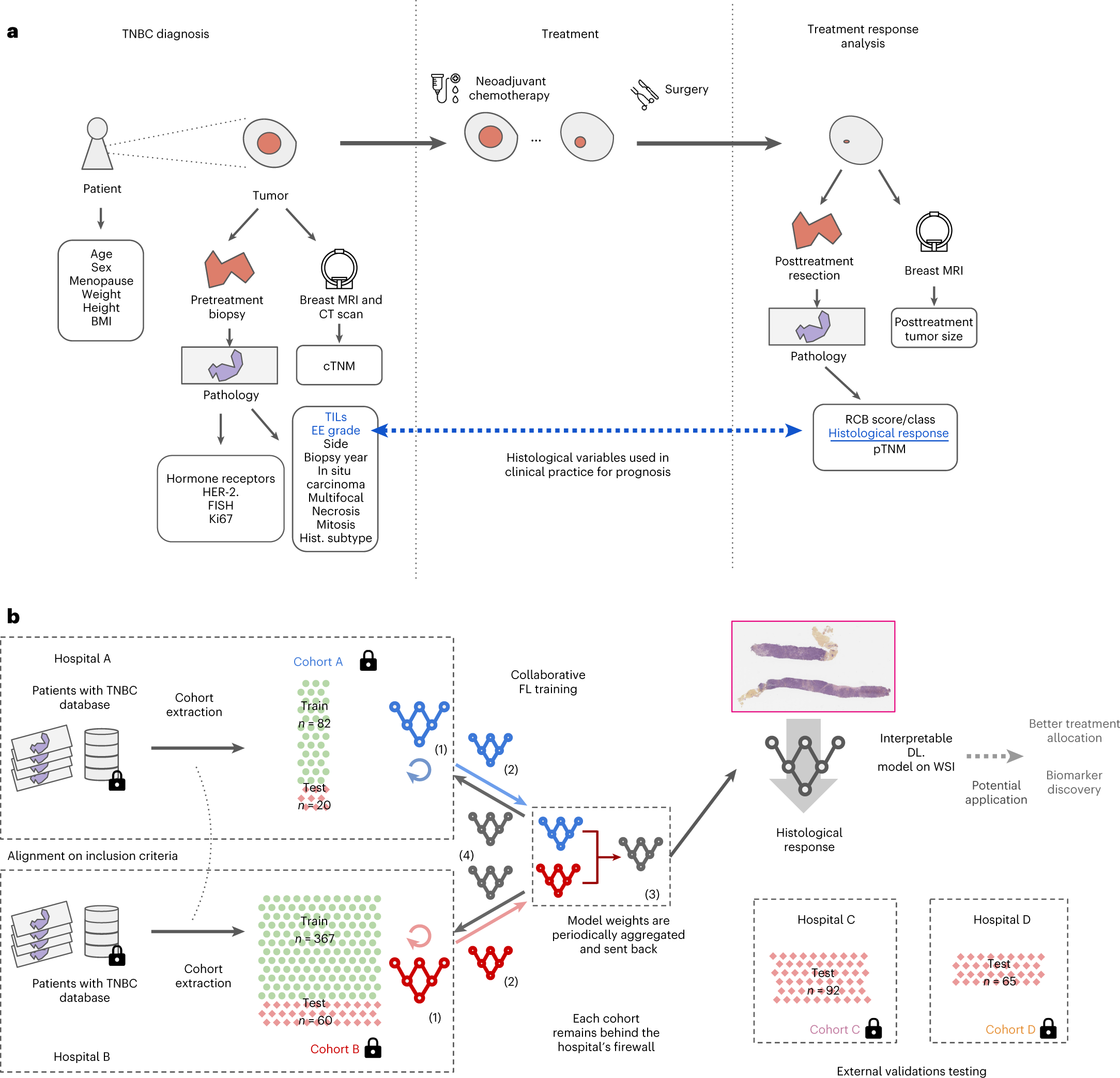
Federated learning for predicting histological response to neoadjuvant chemotherapy in triple-negative breast cancer | Nature Medicine
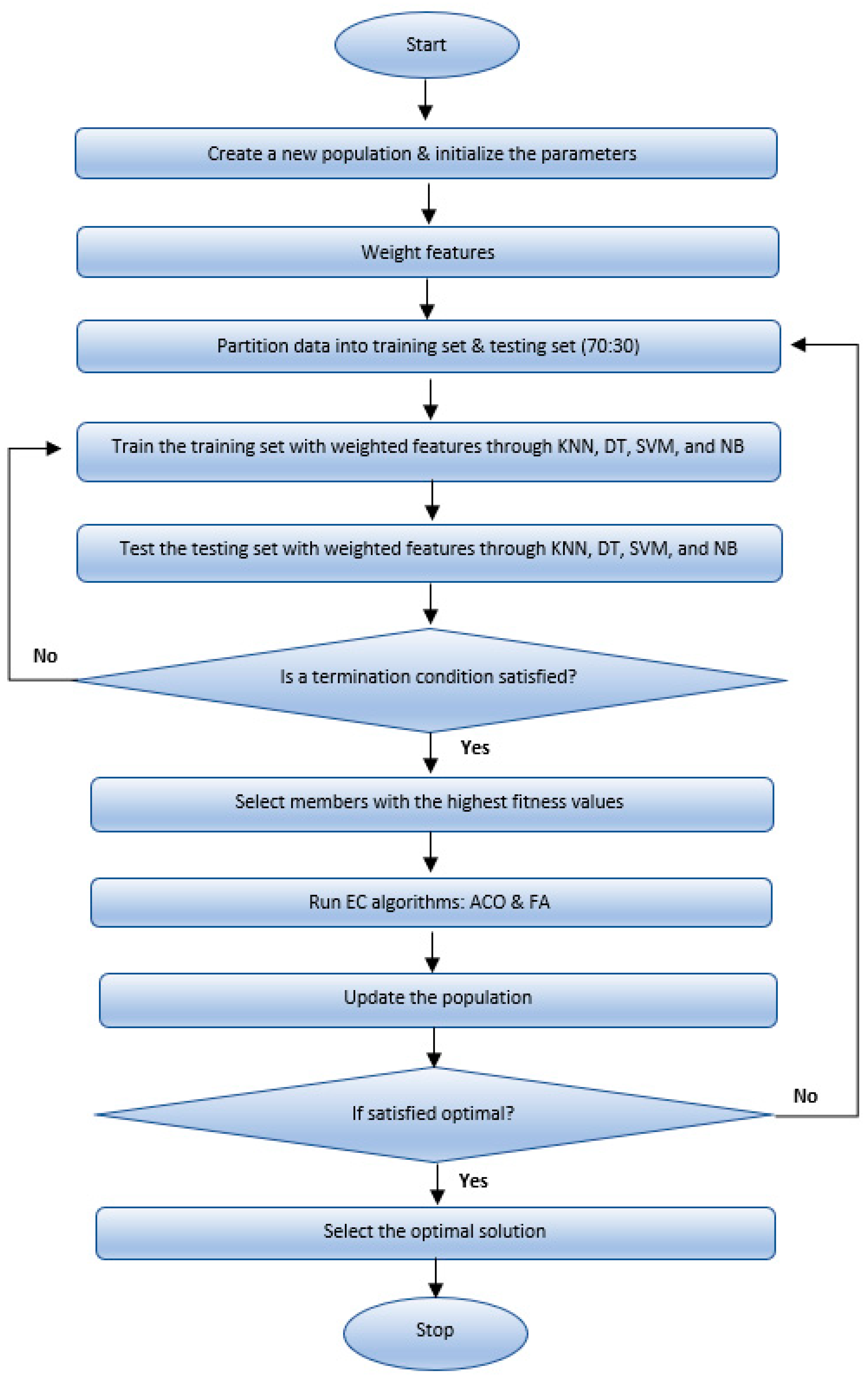
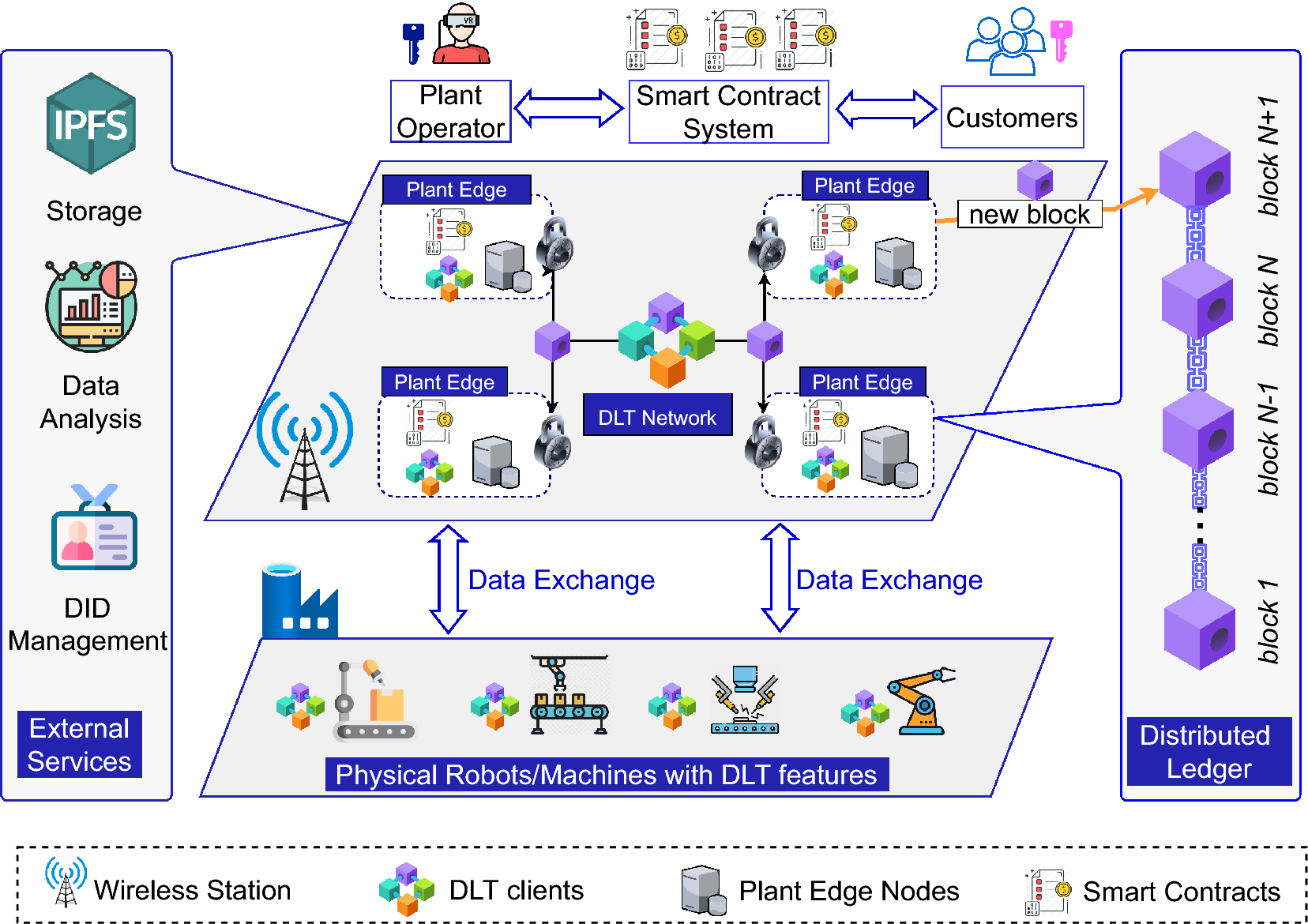
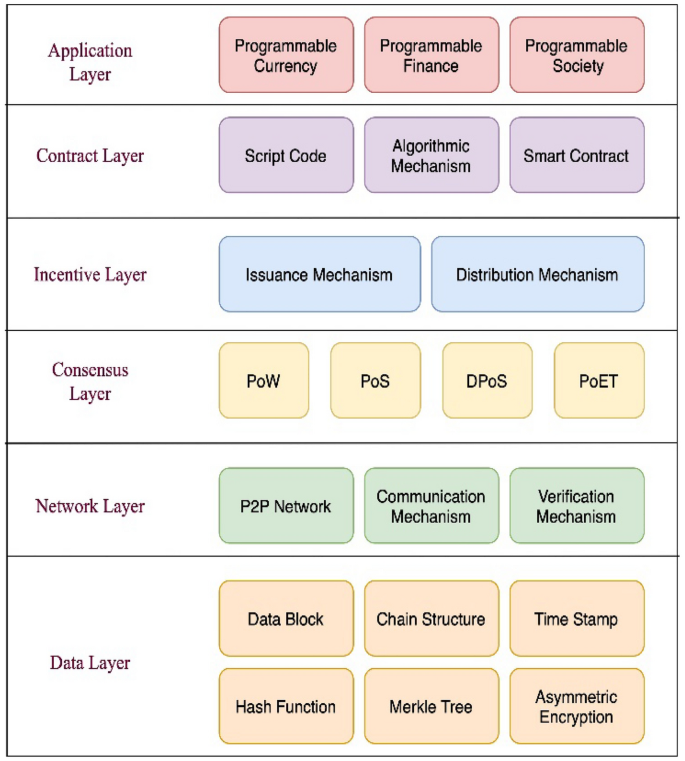
Mathematics | Free Full-Text | Supervised Learning by Evolutionary Computation Tuning: An Application to Blockchain-Based Pharmaceutical Supply Chain Cost Model
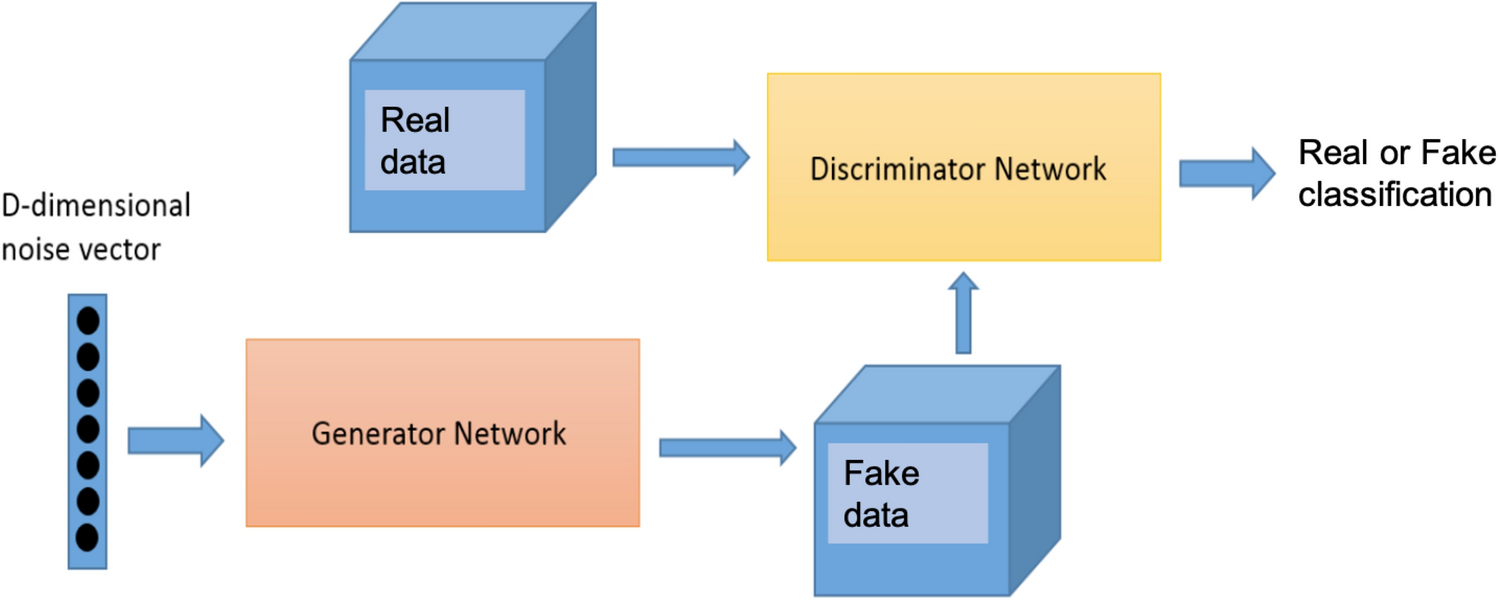
Synthetic flow-based cryptomining attack generation through Generative Adversarial Networks | Scientific Reports

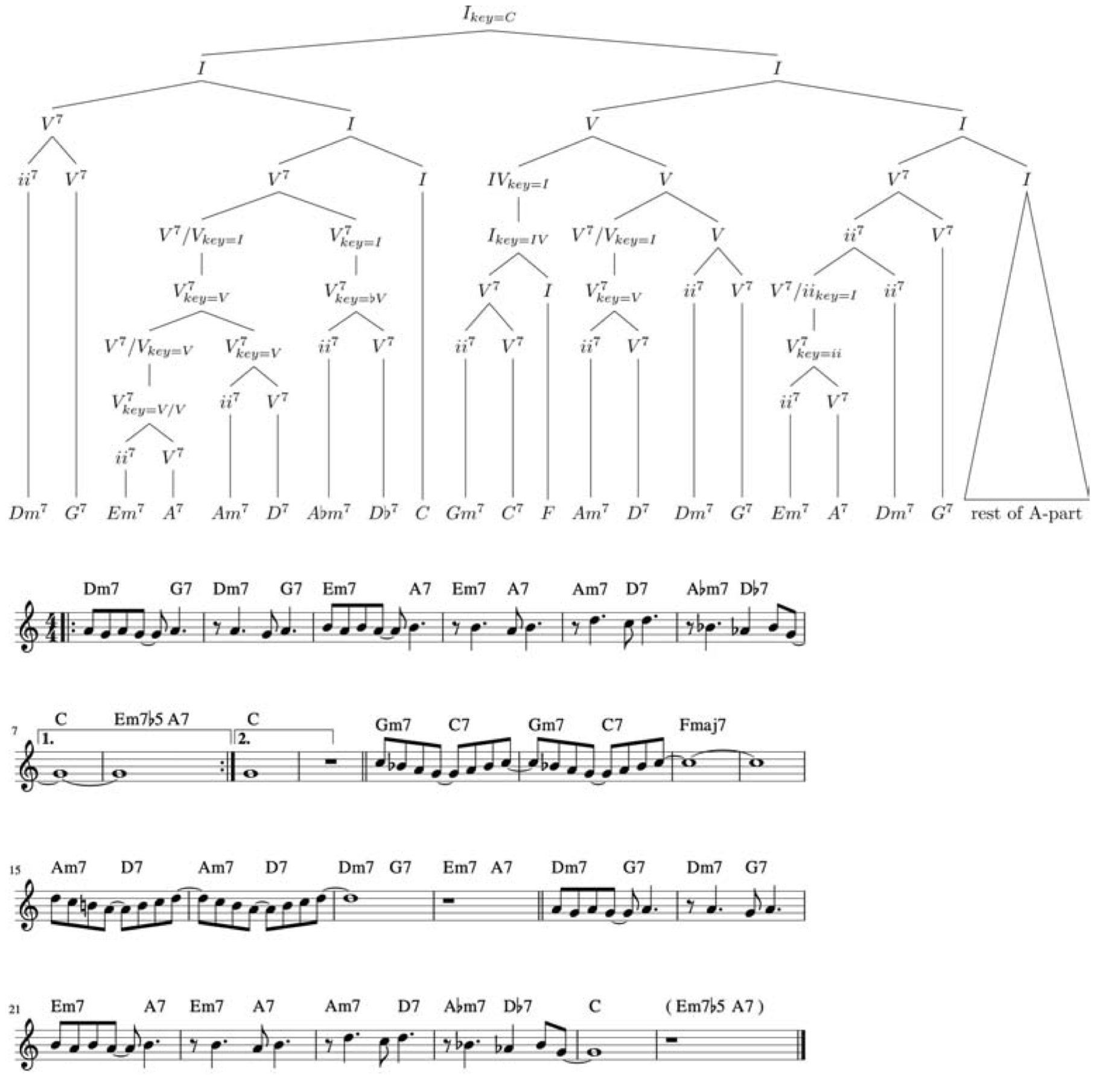
Alfred's Essentials of Music Theory, Complete (Lessons * Ear Training * Workbook)-------------- (CD's Not Included): Surmani, Andrew, Surmani, Karen Farnum, Manus, Morton: 9780882848976: Amazon.com: Books
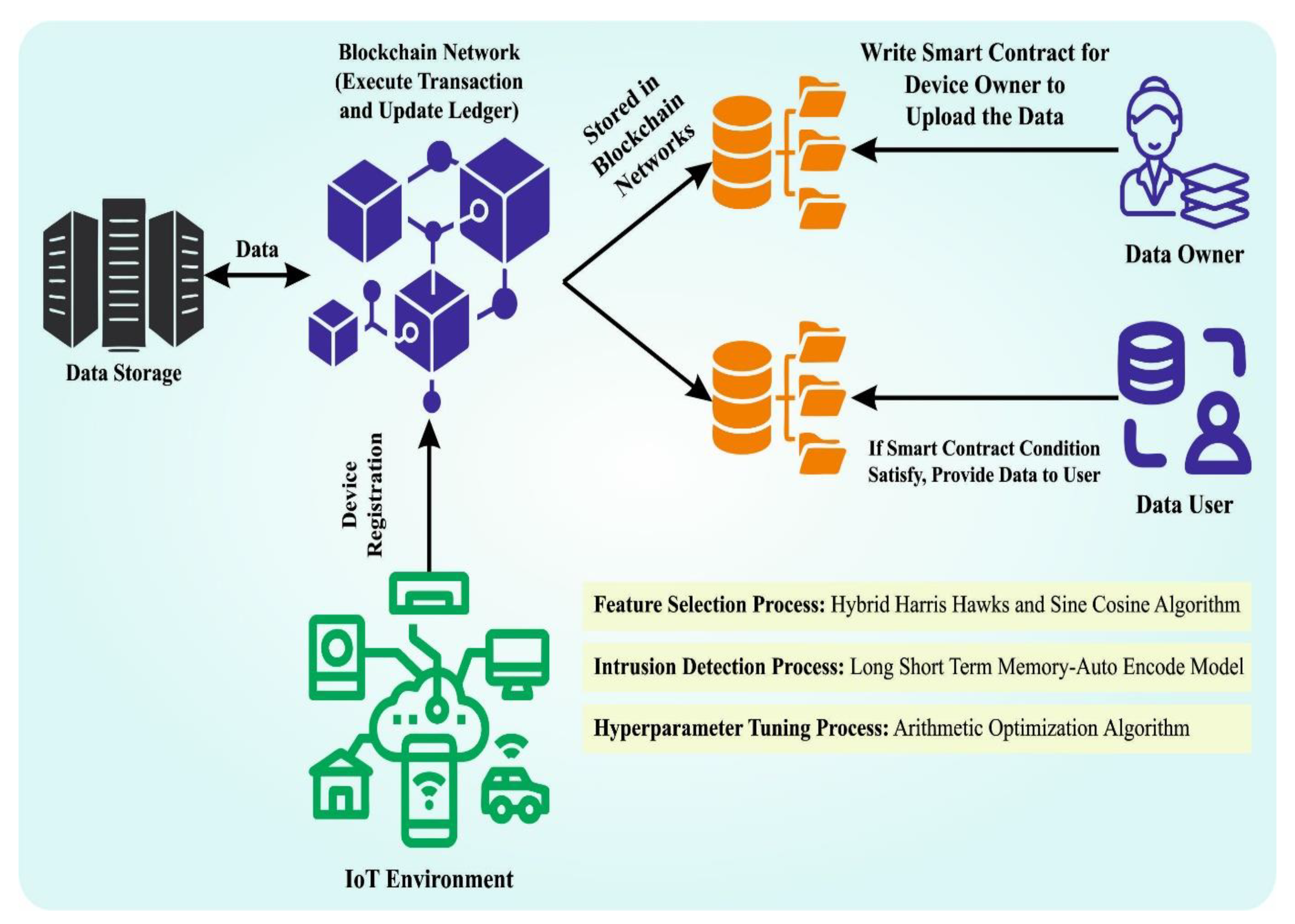
Mathematics | Free Full-Text | Blockchain-Assisted Hybrid Harris Hawks Optimization Based Deep DDoS Attack Detection in the IoT Environment
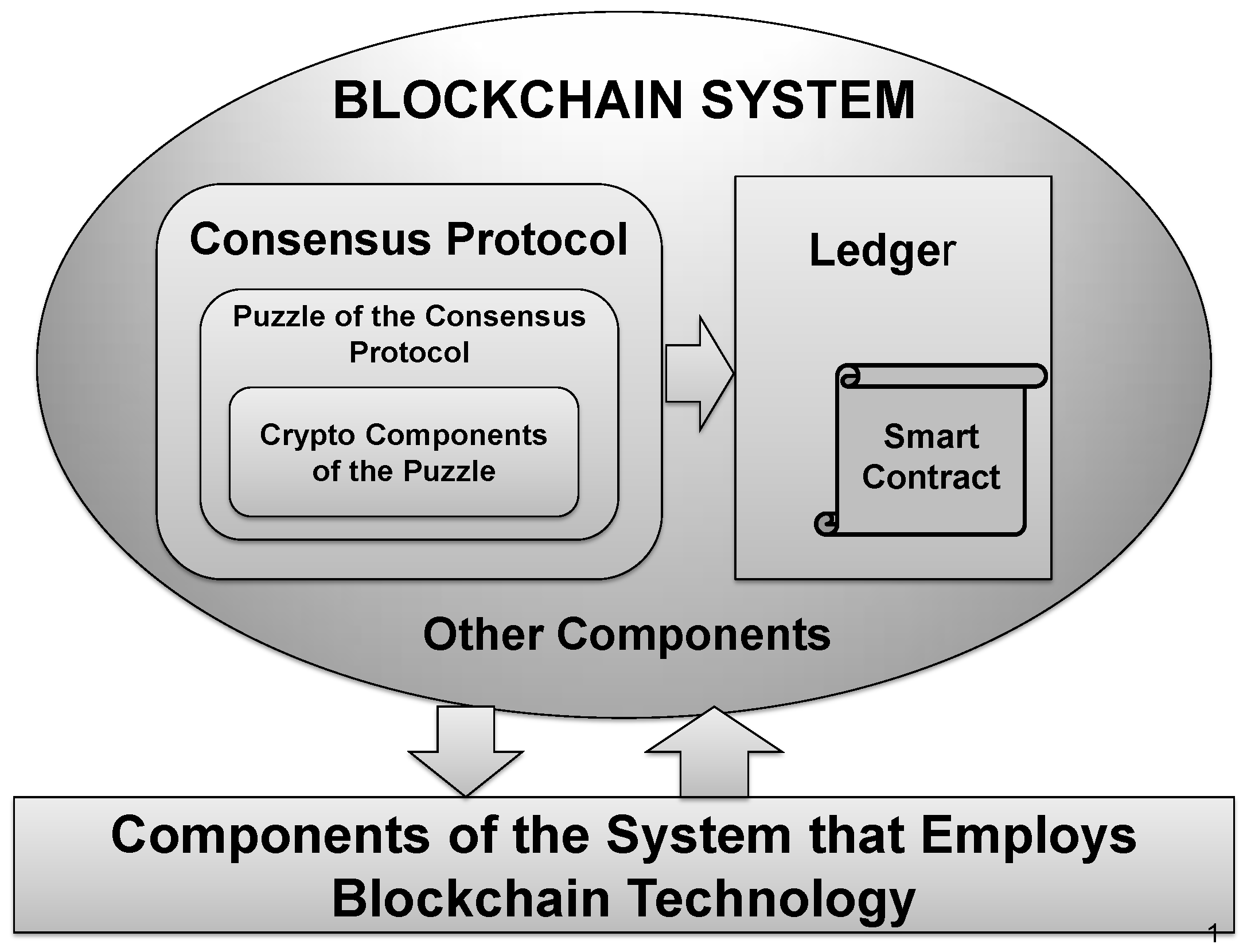
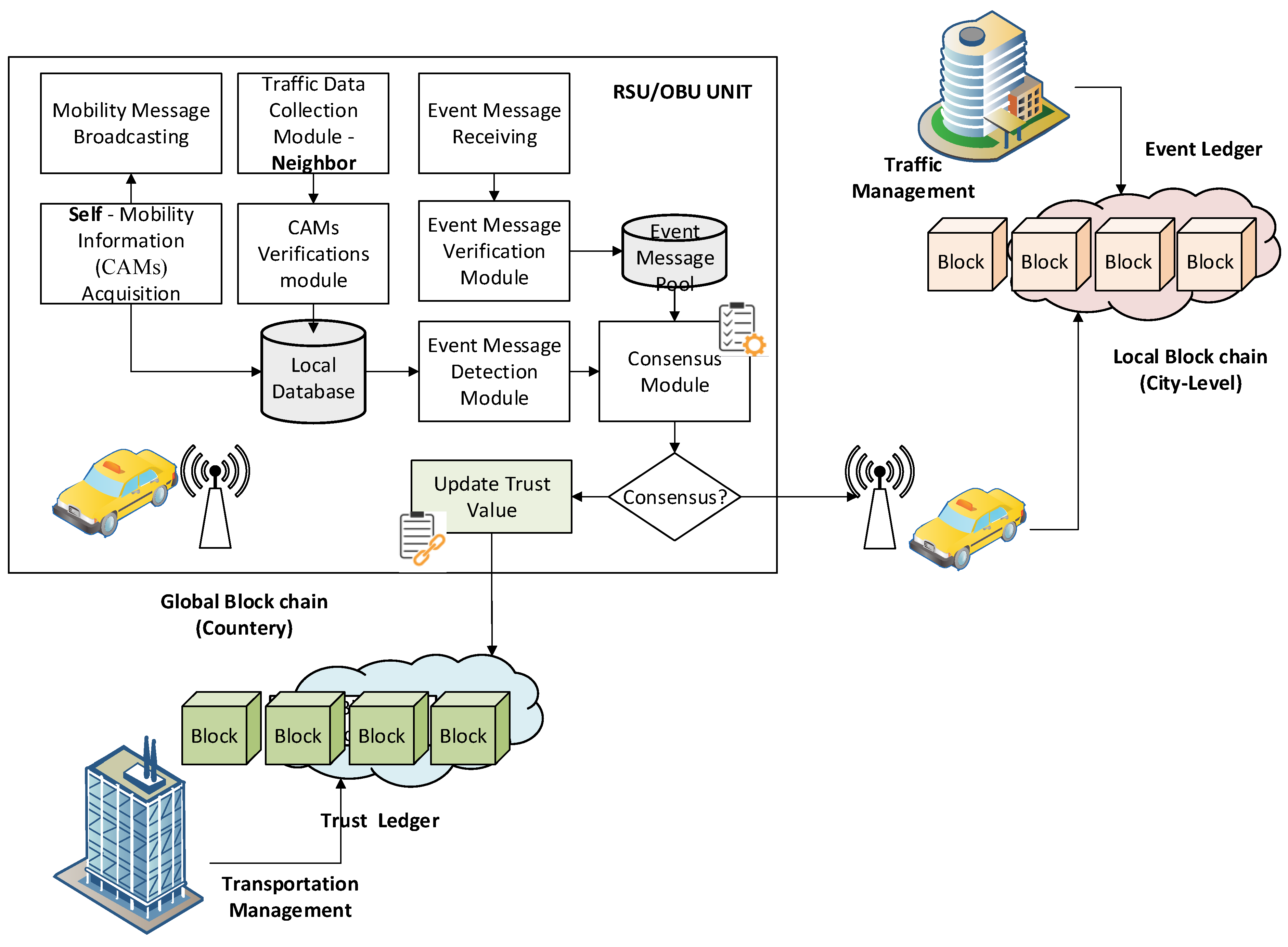
Symmetry | Free Full-Text | An Approach for Blockchain and Symmetric Keys Broadcast Encryption Based Access Control in IoT